Access token can be retrieve in different ways. This blog is explained the way you can get access token using cURL command. As a next step, I'm going to explain the way you can retrieve an access token using Advance REST client(Firefox plugin).
Step 1 :-
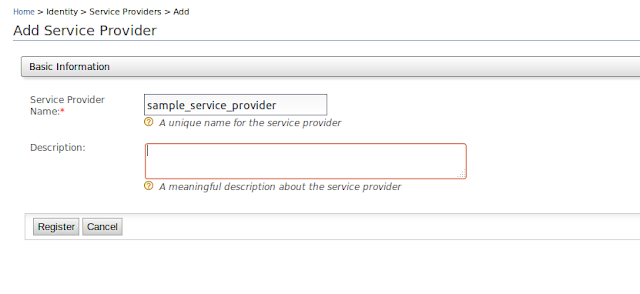
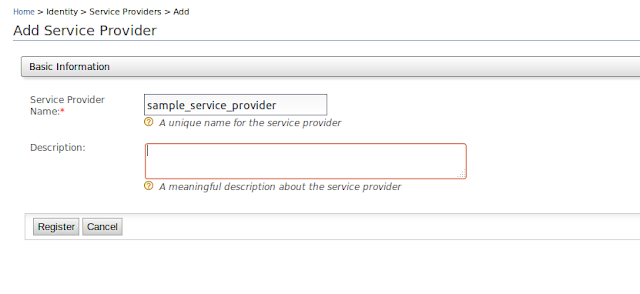
First create a service provider in WSO2 Identity server.
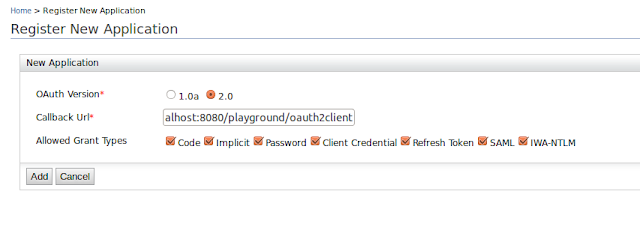
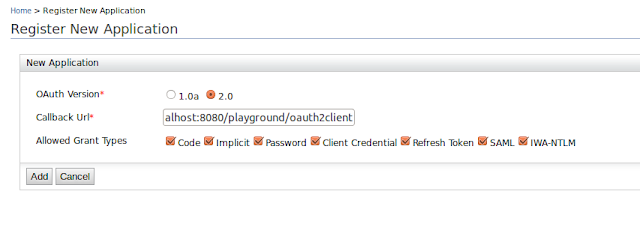
Register a new application by providing callback url and allowed grant types. You must tick a password grant type because I'm going to get an access token using password grant type
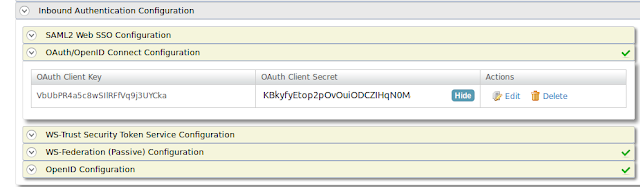
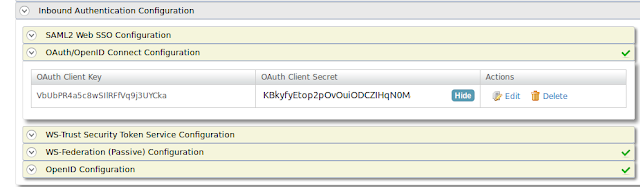
After above configurations are done. You can see the generated client key and secret as below
Now you have client key and client secret for particular application. That means, you have completed the first step.
Step 2 :-
Get the base64 encoded value for client key and secret. before get the encoded value, client key and secret should be separated by colon.
<client_key>:<client_secret>
VbUbPR4a5c8wSIlRFfVq9j3UYCka:KBkyfyEtop2pOvOuiODCZIHqN0Ma
This is the base64 encoded value for above string.
VmJVYlBSNGE1Yzh3U0lsUkZmVnE5ajNVWUNrYTpLQmt5ZnlFdG9wMnBPdk91aU9EQ1pJSHFOME1h
Step 3 :-
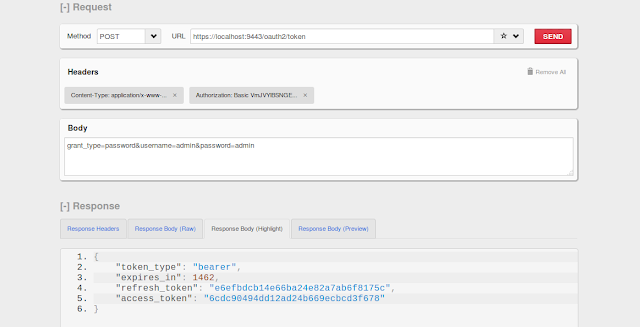
Install advance REST client in to Firefox.
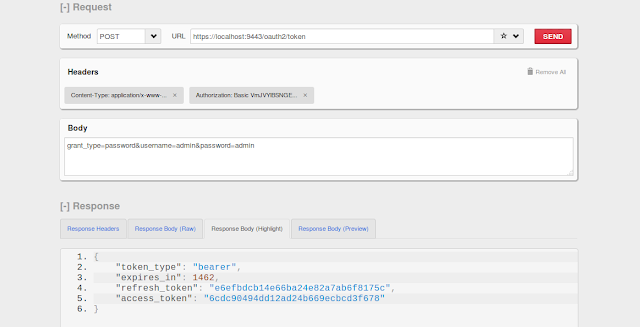
Select Method as POST
URL :- https://localhost:9443/oauth2/token
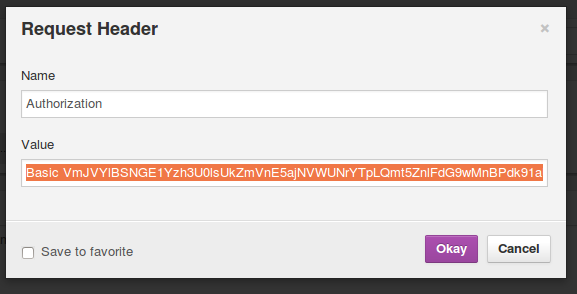
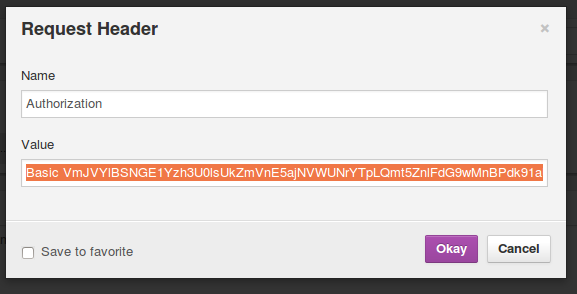
Click on headers and add custom header as below
Name :- Authorization
Value :- Basic VmJVYlBSNGE1Yzh3U0lsUkZmVnE5ajNVWUNrYTpLQmt5ZnlFdG9wMnBPdk91aU9EQ1pJSHFOME1h
Add content type as a custom header
Name :- Content-Type
Value :- application/x-www-form-urlencoded

Add rest of the url in to the body
grant_type=password&username=admin&password=admin
and click on the send button. You could see below result with the required response.
Step 1 :-
First create a service provider in WSO2 Identity server.
Register a new application by providing callback url and allowed grant types. You must tick a password grant type because I'm going to get an access token using password grant type
After above configurations are done. You can see the generated client key and secret as below
Now you have client key and client secret for particular application. That means, you have completed the first step.
Step 2 :-
Get the base64 encoded value for client key and secret. before get the encoded value, client key and secret should be separated by colon.
<client_key>:<client_secret>
VbUbPR4a5c8wSIlRFfVq9j3UYCka:KBkyfyEtop2pOvOuiODCZIHqN0Ma
This is the base64 encoded value for above string.
VmJVYlBSNGE1Yzh3U0lsUkZmVnE5ajNVWUNrYTpLQmt5ZnlFdG9wMnBPdk91aU9EQ1pJSHFOME1h
Step 3 :-
Install advance REST client in to Firefox.
Select Method as POST
URL :- https://localhost:9443/oauth2/token
Click on headers and add custom header as below
Name :- Authorization
Value :- Basic VmJVYlBSNGE1Yzh3U0lsUkZmVnE5ajNVWUNrYTpLQmt5ZnlFdG9wMnBPdk91aU9EQ1pJSHFOME1h
Add content type as a custom header
Name :- Content-Type
Value :- application/x-www-form-urlencoded

Add rest of the url in to the body
grant_type=password&username=admin&password=admin
and click on the send button. You could see below result with the required response.
Comments
Post a Comment