This blog explained the way to test the passive sts in wso2 identity server. I'm using wso2 identity server 5.0.0 with service pack1.
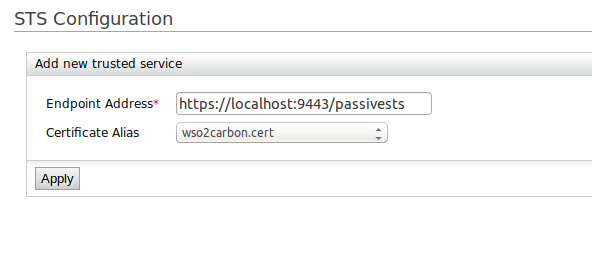
Select the 'WS-Trust Security Token Service Configuration', click configure and add new trusted service as below.
After you completed the configuration, go to this url : http://localhost:8080/PassiveSTSSampleApp/ and log in to the app.
Step 1 :-
Checkout this sample[1] and build it.
sudo svn checkout http://svn.wso2.org/repos/wso2/carbon/platform/branches/turing/products/is/5.0.0/modules/samples/passive-sts/ passive-sts
mvn clean install
Step 2 :-
Deploy PassiveSTSSampleApp.war file which is created in /home/madura/Documents/issues/UNISUPERDEV-25/passive-sts/passive-sts-client/PassiveSTSSampleApp/target directory. You can use external tomcat server for deployment. If not you can use the tomcat server located in IS
Step 3 :-
IDP configurations
Click ‘Add’ under ‘Service Providers’ in the ‘Main’ tab.
Specify any name as the service provider name. We have used passivests here.
Click ‘Add’ under ‘Service Providers’ in the ‘Main’ tab.
Specify any name as the service provider name. We have used passivests here.
Select the 'WS-Trust Security Token Service Configuration', click configure and add new trusted service as below.
Under ‘Inbound Authentication Configuration’ expand ‘WS-Federation (Passive) Configuration’.
For 'Service Realm Name' give the same identifier as we given as realm in Web app
e.g :-
PassiveSTSSampleApp
5. Add claims which need to show in the sample app
After you completed the configuration, go to this url : http://localhost:8080/PassiveSTSSampleApp/ and log in to the app.



Comments
Post a Comment